Today, data is everywhere. We spend the majority of our work lives with our computers connected to the world-wide-web, leaving our data especially vulnerable. But knowing is only half the battle of data security. Here are 5 “Do’s” that will help keep your information secure.
- Do back up your data. We have an in depth post on the importance of back ups and the way you can select the best backup provider for your business.Want to find out how much lost data or downtime would cost you? Check out our new Recovery Time Calculator.
- Do password protect your sensitive files and devices. Use a strong password (minimum 8 characters, with capitals, lowercase letters, and numbers) that is not easily guessed. The longer the password, the more secure you will be.Don’t believe that more characters equals more security? Try this tool that estimates how long it would take a computer to guess your login information. A strong password is the best defense for keeping sensitive data out of the hands of hackers.
- Do use anti-virus software. Passwords are great, but won’t usually stop a virus if you’re infected while you’re logged into your PC. This is where anti-virus software plays a critical role in security.By identifying and alerting you of threats, good (and constantly updated) anti-virus programs give you the opportunity (if they don’t do it automatically) to eliminate threats as soon as they are detected and before they can take anything valuable.
- Do keep programs such as Java, Flash, Chrome, Firefox, and even your operating system as up to date as possible. Their pop-up notifications may be annoying, but they are for a good cause. The updates they contain are very important. Most programs are updated to address security concerns and potential performance issues, so it is in your best interest to act quickly and install critical updates.For our managed clients, we test and update these programs to keep them running as safely as possible.
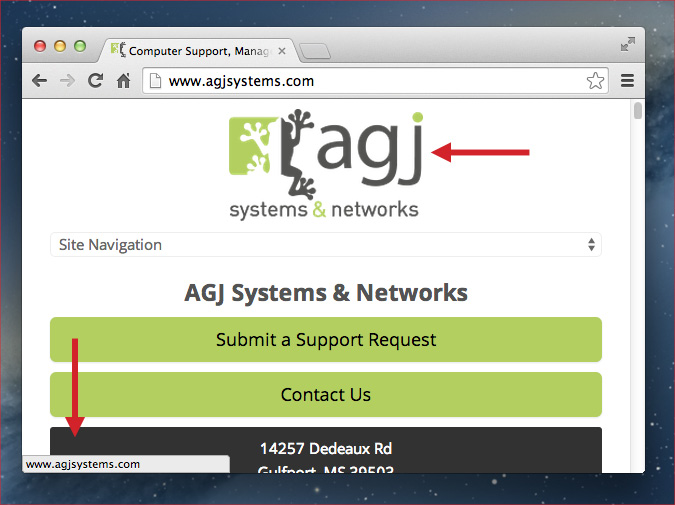
- Do remain cautious of emails and links that appear suspicious. Most browsers display the address behind a link in the bottom corner of the screen, as you can see in this image.So pay attention to those previews before you click through a link. If the link won’t lead to where you think it should, steer clear. PC World does a great job of explaining this in more detail.
Subscribe to our blog on the right of this page for more posts like this, including a forthcoming post on the top five “do-nots” concerning data security.
To learn more about data security, head over to our website where we deal with issues of information security and data protection.