Defend Against CryptoLocker Malware Threat: Secure Your Data
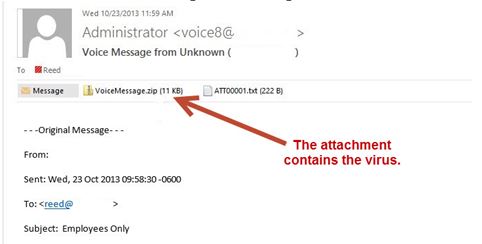
The latest variant is disguised as a voicemail message which contains a zip file. Do not click on attachments from companies you don't know or from which you haven't expressed interest in receiving information.
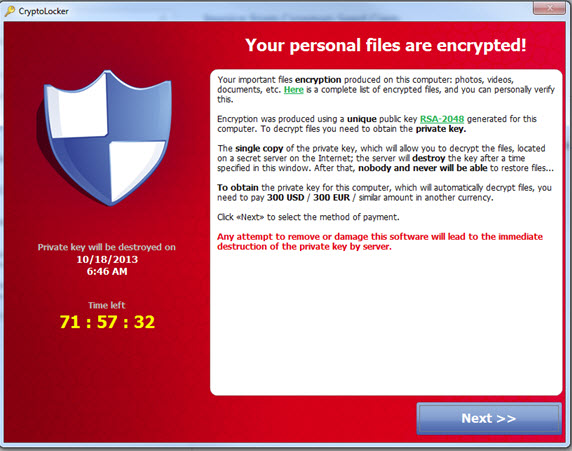
You may have heard of a new malware infection that has recently been making the rounds called CryptoLocker. Many antivirus and anti-malware programs have had a difficult time blocking this malware. If you become infected, Cryptolocker encrypts the files on your PC and any network drives you're connected to, which renders them impossible to open unless you "purchase" a decryption key from the hijackers typically for a fee of $300.
While we have a multi-layered security approach set up for our business clients that will reduce the likelihood of getting CryptoLocker, education is the key to avoiding this malware.
If you see this or a similar pop-up message on your screen, call us immediately:
How is the CryptoLocker virus spread?
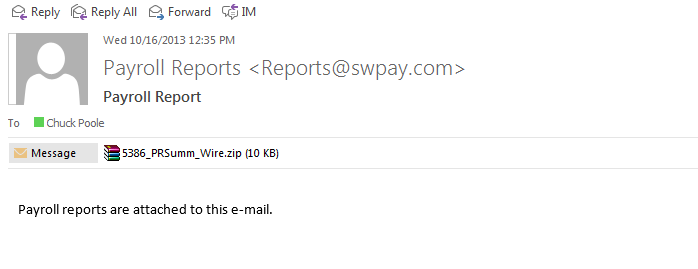
CryptoLocker is spread through phony emails designed to look like they’re from legitimate businesses and fake FedEx and UPS tracking notifications. Once opened, CryptoLocker installs itself in the “Documents and Settings” folder, scans the hard drive and encrypts your files. Then CryptoLocker launches a pop-up window with the 100-hour countdown and provides details on how to pay the ransom. Email attacks are fairly easy to avoid: take extreme care with attachments you weren't expecting (even if from people you know), or from people you don't know well. Here is a common email we see that tries to get the user to open a file attachment:
How can I protect myself, my network and my business from CryptoLocker?
Security companies are actively working on a protection for this specific virus, but there isn’t one just yet. Here are some tips that you can follow to protect yourself from this virus:
- Since the biggest threat from CryptoLocker is losing your important files, take regular backups! If you can, store your backup’s remotely or offline then they can’t be affected in the event of an attack on your active files. Your backups will be rendered useless if they are scrambled by CryptoLocker along with the primary copies of the files.
- Use multilayered antivirus software for your computer and ensure that it remains active and updated.
- Double-check the legitimacy of links received in emails and social media messages. Never open unknown or unwanted emails with attachments, especially those that come from banks and other financial institutions. Have a proper anti-phishing and anti-spam protection installed to filter out the fraudulent emails.
- Keep your operating system and software up to date with patches. This lessens the chance of malware sneaking onto your computer unnoticed through security holes.
- Review the access control settings on any network shares you have, whether at home or at work. Don’t grant yourself or anyone else write access to files that you only need to read. Don’t grant yourself any access at all to files that you don’t need to see – that stops malware seeing and stealing them, too.
- Don’t give administrative privileges to your user accounts. Privileged accounts with administrative privileges can reach much further and more destructively both on your own hard disk and across the network.
- If you have any questions about CryptoLocker or are worried that you may not be doing everything you can to protect yourself, your network and your business from this scary virus, give us a call and we can advise you on additional steps to take to protect yourself and your data, files and images.
Please let me know if you have any questions or concerns, and feel free to forward this email to friends or colleagues.
Regards,
Ryan Giles
AGJ Systems

Brooks Holstein
LifeCare Properties LLC

Cindy Duvall
External Communications Manager
Mississippi Power